– America; The Not So Free (Veterans Today, June 9, 2013)
PRISM
Meet ‘PRISM’ Whistleblower Edward Snowden The Source Behind The Biggest Intelligence Leak In NSA History (Video)
Related info:
– Obama Regime To Shoot The PRISM-Gate Messenger, Launches Criminal Probe Into NSA Leaks
MUST-SEE!
The 29-year-old source behind the biggest intelligence leak in the NSA’s history explains his motives, his uncertain future and why he never intended on hiding in the shadows
– Edward Snowden: the whistleblower behind the NSA surveillance revelations (Guardian, June 9, 2013):
Glenn Greenwald, Ewen MacAskill and Laura Poitras in Hong Kong
The individual responsible for one of the most significant leaks in US political history is Edward Snowden, a 29-year-old former technical assistant for the CIA and current employee of the defence contractor Booz Allen Hamilton. Snowden has been working at the National Security Agency for the last four years as an employee of various outside contractors, including Booz Allen and Dell.
The Guardian, after several days of interviews, is revealing his identity at his request. From the moment he decided to disclose numerous top-secret documents to the public, he was determined not to opt for the protection of anonymity. “I have no intention of hiding who I am because I know I have done nothing wrong,” he said.
Snowden will go down in history as one of America’s most consequential whistleblowers, alongside Daniel Ellsberg and Bradley Manning. He is responsible for handing over material from one of the world’s most secretive organisations – the NSA.
In a note accompanying the first set of documents he provided, he wrote: “I understand that I will be made to suffer for my actions,” but “I will be satisfied if the federation of secret law, unequal pardon and irresistible executive powers that rule the world that I love are revealed even for an instant.”
Despite his determination to be publicly unveiled, he repeatedly insisted that he wants to avoid the media spotlight. “I don’t want public attention because I don’t want the story to be about me. I want it to be about what the US government is doing.”
He does not fear the consequences of going public, he said, only that doing so will distract attention from the issues raised by his disclosures. “I know the media likes to personalise political debates, and I know the government will demonise me.”
Despite these fears, he remained hopeful his outing will not divert attention from the substance of his disclosures. “I really want the focus to be on these documents and the debate which I hope this will trigger among citizens around the globe about what kind of world we want to live in.” He added: “My sole motive is to inform the public as to that which is done in their name and that which is done against them.”
He has had “a very comfortable life” that included a salary of roughly $200,000, a girlfriend with whom he shared a home in Hawaii, a stable career, and a family he loves. “I’m willing to sacrifice all of that because I can’t in good conscience allow the US government to destroy privacy, internet freedom and basic liberties for people around the world with this massive surveillance machine they’re secretly building.”
‘I am not afraid, because this is the choice I’ve made’
CISPA Will Legalize PRISM NSA Spy Program
– CISPA Will Legalize PRISM Spy Program (Activist Post, June 8, 2013):
Give them an inch and they will take a mile. That is how power-hungry tyrants interpret any law.
The PATRIOT Act and the FISA court led to the blanket wiretapping of every American citizen and a PRISM lens into all Internet activity for the NSA.
NSA’s ‘Boundless Informant’ Collects 3 Billion Intelligence Pieces From US Computer Networks In One Month
– The NSA’s “Boundless Informant” Collects 3 Billion Intelligence Pieces From US Computer Networks In One Month (ZeroHedge, June 8, 2013):
There’s one reason why the administration, James Clapper and the NSA should just keep their mouths shut as the PRISM-gate fallout escalates: with every incremental attempt to refute some previously unknown facet of the US Big Brother state, a new piece of previously unleaked information from the same intelligence organization now scrambling for damage control, emerges and exposes the brand new narrative as yet another lie, forcing even more lies, more retribution against sources, more journalist persecution and so on.The latest piece of news once again comes from the Guardian’s Glenn Greenwald who this time exposes the NSA’s datamining tool “Boundless Informant” which according to leaked documents collected 97 billion pieces of intelligence from computer networks worldwide in March 2013 alone, and “3 billion pieces of intelligence from US computer networks over a 30-day period.”
This is summarized in the chart below which shows that only the middle east has more active NSA-espionage than the US. Also, Obama may not want to show Xi the activity heatmap for China, or else the whole “China is hacking us” script may promptly fall apart.
Using simple, non-AES 256 breaking math, 3 billion per month amounts to some 100 million intrusions into the US per day, or looked at from another perspective, just a little more than the “zero” which James Clapper vouched announced earlier today is the applicable number of US citizens falling under the NSA’s espionage mandate: “Section 702 cannot be used to intentionally target any U.S. citizen, or any other U.S. person, or to intentionally target any person known to be in the United States.” Oops.
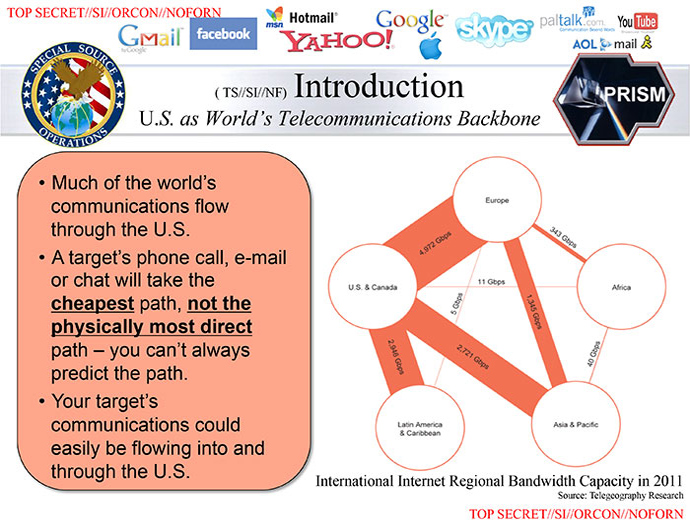
But it gets worse for the NSA. As the Guardian reports, “Emmel, the NSA spokeswoman, told the Guardian: “Current technology simply does not permit us to positively identify all of the persons or locations associated with a given communication (for example, it may be possible to say with certainty that a communication traversed a particular path within the internet. It is harder to know the ultimate source or destination, or more particularly the identity of the person represented by the TO:, FROM: or CC: field of an e-mail address or the abstraction of an IP address). Thus, we apply rigorous training and technological advancements to combine both our automated and manual (human) processes to characterize communications – ensuring protection of the privacy rights of the American people. This is not just our judgment, but that of the relevant inspectors general, who have also reported this.”
In other words, Americans are absolutely the target of billions of monthly intrusions, but said data “mining” is exempted because it is difficult to identify in advance if a US citizen is implicated in any metadata chain.
Only it isn’t as it is the whole premise behind Boundless Informant.
FLASHBACK: Barack Obama’s Speech On Warrantless Wiretapping In 2007! (Video)
Change!
– Flashback to 2007: Obama’s Speech on Warrantless Wiretapping (Liberty Blitzkrieg, June 7, 2013):
At this point we all understand that there is absolutely zero in common with Presidential-candidate Barack Obama and President Barack Obama.
He has so consistently lied while in office I have become convinced that he ranks deception as one of his most cherished hobbies.
Right up there with rounds of golf and posing for pictures with ice cream cones (he learned that trick from Uncle Warren). After all, the man’s entire life is a giant lie.
A constitutional law professor who spends his entire two terms dismantling the document itself.
So… just in case you need a reminder in light of the NSA/Verizon spy scandal, here is what candidate Obama was saying in 2007.
10 Questions: Warrantless Wiretaps
YouTube
Martin Luther King: ‘Everything Adolf Hitler Did In Germany Was Legal”’
– Martin Luther King: “Everything Adolf Hitler did in Germany was Legal” (Liberty Blitzkrieg, June 7, 2013):
Even if you have read Martin Luther King’s celebrated “Letter from Birmingham Jail,” I insist you read it again. For those that have never read it, the inspired prose may very well change your life. The letter’s message is eternal and extraordinarily relevant in the current global struggle of the 99.9% against the criminality, corruption and oppression of a very small, but very powerful 0.01%. One of the key tactics this tiny minority uses is to claim that their immoral deeds are “legal.” He spends much of his time in the letter outlining the distinction between “just laws” and an “unjust laws,” and one of the key points he makes that we should all keep close to our hearts and minds in these trying times is:
We should never forget that everything Adolf Hitler did in Germany was “legal” and everything the Hungarian freedom fighters did in Hungary was “illegal.” It was “illegal” to aid and comfort a Jew in Hitler’s Germany. Even so, I am sure that, had I lived in Germany at the time, I would have aided and comforted my Jewish brothers.
I also think it’s important to recognize that many of his contemporaries referred to his tactics as “extremist,” very similar to how the term “terrorist” is used currently to demonize public dissent in America. Below are some of the excepts I found most powerful:
Read moreMartin Luther King: ‘Everything Adolf Hitler Did In Germany Was Legal”’
Google, Facebook, Skype, Yahoo And AOL Blatantly Lying To Users In Denying NSA Spy Grid Scheme PRISM
Related info:
– UK’s Electronic Eavesdropping And Security Agency GCHQ Also Accesses NSA’s Secret PRISM Programme
– Obama Regime To Shoot The PRISM-Gate Messenger, Launches Criminal Probe Into NSA Leaks
– President Obama Defends Unconstitutional Surveillance Programs In San Jose Speech
– How Google, Facebook, Skype, Yahoo and AOL are all blatantly lying to their own users in denying NSA spy grid scheme (Natural News, June 8, 2013):
What do Google, AOL, Skype, Facebook, Apple, Hotmail and Yahoo all have in common? They have all been caught turning over private user data to the government’s spy agency, the NSA. All these companies routinely turn over the emails, voice calls, text chats, photos, files and even logins and passwords of their users, including Americans.
“There is a massive apparatus within the United States government that with complete secrecy has been building this enormous structure that has only one goal,” journalist Glenn Greenwald recently told Piers Morgan (who knows all about spying and hacking people’s private data). “And that is to destroy privacy and anonymity not just in the United States but around the world.”
Tech companies rush to issue (false) denials
Obama Regime To Shoot The PRISM-Gate Messenger, Launches Criminal Probe Into NSA Leaks
– Shoot The PRISM-Gate Messenger: Obama To Launch Criminal Probe Into NSA Leaks (ZeroHedge, June 7, 2013):
Suddenly embroiled in too many scandals to even list, and humiliated by a publicly-exposed (because everyone knew about the NSA superspy ambitions before, but with one major difference: it was a conspiracy theory…. now it is a conspiracy fact) surveillance scandal that makes Tricky Dick look like an amateur, earlier today, as expected, Obama came out and publicly declared “I am not a hacker” and mumbled something about “security”, “privacy” and “inconvenience.” He went on to explain how the government “welcomes the debate” of all three in the aftermath of the public disclosure that every form of electronic communication is intercepted and stored by the US government (now that said interception is no longer secret, of course) but more importantly how it is only the government, which is naturally here to help, that should be the ultimate arbiter in deciding what is best for all.Yet the PRISM-gate scandal which is sure to only get worse with time as Americans slowly realize they are living in a Orwellian police state, meant Obama would have to do more to appease a public so furious even the NYT issued a scathing editorial lamenting the obliteration of Obama’s credibility. Sure enough, the president did. Reuters reports that the first course of action by the US government will be to… shoot the messenger.
Reuters reports that “President Barack Obama’s administration is likely to open a criminal investigation into the leaking of highly classified documents that revealed the secret surveillance of Americans’ telephone and email traffic, U.S. officials said on Friday.”
And how did Reuters learn this: from “law enforcement and security officials who were not authorized to speak publicly.”
The mimetic absurdity of the narrative is just too surreal to even contemplate for more than a minute before bursting out in laughter: the administration’s plans to launch criminal charges against those who “leaked” its Nixonian espionage masterplan involving every US (and world) citizen using the Internet, revealed by another group of sources leaking in secret. Pure poetry.
Read moreObama Regime To Shoot The PRISM-Gate Messenger, Launches Criminal Probe Into NSA Leaks
President Obama & America’s Internet Companies Are ALL LYING – Here Is How Your Data Is Handed Over To Uncle Sam
– “You Should Use Both” – How America’s Internet Companies Are Handing Over Your Data To Uncle Sam (ZeroHedge, June 8, 2013):
In the aftermath of the PRISM spying scandal, the first and logical response was an expected one: lie. The president did it, and so did the various companies implicated in the biggest US surveillance scandal ever exposed. To wit:
- Zuckerberg: “Facebook is not and has never been part of any program to give the US or any other government direct access to our servers.”
- Google CEO Larry Page: “We have not joined any program that would give the US government – or any other government – direct access to our servers.”
- Yahoo: “We do not provide the government with direct access to our servers, systems, or network.”
One small problem: they are all lying.
The NYT explains just how the explicit handover of private customer data from Corporate Server X to NSA Server Y takes place.
The companies that negotiated with the government include Google, which owns YouTube; Microsoft, which owns Hotmail and Skype; Yahoo; Facebook; AOL; Apple; and Paltalk, according to one of the people briefed on the discussions. The companies were legally required to share the data under the Foreign Intelligence Surveillance Act. People briefed on the discussions spoke on the condition of anonymity because they are prohibited by law from discussing the content of FISA requests or even acknowledging their existence.
In at least two cases, at Google and Facebook, one of the plans discussed was to build separate, secure portals, like a digital version of the secure physical rooms that have long existed for classified information, in some instances on company servers. Through these online rooms, the government would request data, companies would deposit it and the government would retrieve it, people briefed on the discussions said.
UK’s Electronic Eavesdropping And Security Agency GCHQ Also Accesses NSA’s Secret PRISM Programme
UK security agency GCHQ gaining information from world’s biggest internet firms through US-run Prism programme

Documents show GCHQ (above) has had access to the NSA’s Prism programme since at least June 2010. Photograph: David Goddard/Getty Images
– UK gathering secret intelligence via covert NSA operation (Guardian, June 7, 2013):
The UK’s electronic eavesdropping and security agency, GCHQ, has been secretly gathering intelligence from the world’s biggest internet companies through a covertly run operation set up by America’s top spy agency, documents obtained by the Guardian reveal.
The documents show that GCHQ, based in Cheltenham, has had access to the system since at least June 2010, and generated 197 intelligence reports from it last year.
The US-run programme, called Prism, would appear to allow GCHQ to circumvent the formal legal process required to seek personal material such as emails, photos and videos from an internet company based outside the UK.
President Obama Defends Unconstitutional Surveillance Programs In San Jose Speech
From the article:
“When it comes to telephone calls, nobody is listening to your telephone calls,” Obama said. “That’s not what this program is about. As was indicated, what the intelligence community is doing is looking at phone numbers and durations of calls — they are not looking at people’s names and they are not looking at content.”
Oh, really?
– Is The U.S. Government Also Monitoring The CONTENT Of Our Phone Calls?
Flashback:
“The man who trades freedom for security does not deserve nor will he ever receive either. “
– Benjamin Franklin
– President Obama defends surveillance programs in San Jose speech (Mercury News, June 7, 2013):
SAN JOSE — President Barack Obama on Friday defended his administration’s mass collection of telephone and Internet records, saying the surveillance is thoroughly overseen by Congress and judges to strike the right balance between security and privacy.
“When I came into this office, I made two commitments that are more important than any commitment I made: number one to keep the American people safe, and number two to uphold the Constitution,” he told reporters who had gathered at San Jose’s Fairmont Hotel to hear him tout California’s implementation of Obamacare, but were more interested in hearing about government surveillance.
“You can’t have 100 percent security and also then have 100 percent privacy and zero inconvenience. We’re going to have to make some choices as a society,” he said. “I think that on balance, we have established a process and a procedure that the American people should feel comfortable about.”Obama made his first public comments about the growing national firestorm over reports that the National Security Agency has been obtaining massive data on Verizon telephone customers, continuing a George W. Bush-era anti-terrorism program. And the Washington Post reported the NSA and the FBI have access to the central servers of nine leading U.S. Internet companies, including Google, Apple, Yahoo and Facebook.
Read morePresident Obama Defends Unconstitutional Surveillance Programs In San Jose Speech
Breaking News: Disclosed Classified Docs Show Vast, Real-Time, Warrantless NSA Online Surveillance
– Disclosed classified docs show vast, real-time, warrantless NSA online surveillance (RT, June 6, 2013):
Classified information obtained by the Washington Post and The Guardian has revealed a massive, warrantless online surveillance system in use by a US military intelligence agency, giving access to Americans’ search history, emails, live chats and more.
The 41-page PowerPoint presentation, which has been verified by both papers and published almost concurrently on Thursday evening, outlines details of a previously undisclosed program known as PRISM, which allows the fabled military intelligence agency to harvest massive amounts of data on everything from electronic correspondence to file transfers.The slides were meant to be declassified in 2036.
According to the documents, the program currently boasts access to some of the largest Internet companies in the world, with Microsoft thought to be the first corporation to sign onto the surveillance arrangement in 2007.
That company’s participation was followed by Yahoo in 2008, Google, Facebook and PalTalk in 2009, YouTube in 2010, Skype and AOL in 2011, and Apple joining in 2012. Meanwhile, cloud storage company Dropbox is described as “coming soon.”
With the participation of those companies, PRISM and thereby Washington intelligence workers have access to the bulk of Americans’ email, video and voice chat, videos, photos, voice-over-IP (Skype) chats, file transfers, social networking details and more.